Assess Everything.
Secure Everything.
NetSight discovers, collects, analyzes, and reports on your entire network infrastructure — CIS compliance, vulnerabilities, lifecycle risk, and firewall policy — in a single automated assessment.
Assessment Pipeline
Five phases. Complete assessment.
From first scan to executive report — automated, repeatable, and AI-enriched.
Discovery
Nmap + SNMP scanning. Find every device.
Collection
SSH & NETCONF pull configs, routes, state.
Analysis
CIS benchmarks, CVE matching, EOL, firewall audit.
Intelligence
AI risk narratives, findings, remediation roadmaps.
Output
Branded PDF, DOCX, PPTX. Ready to share.
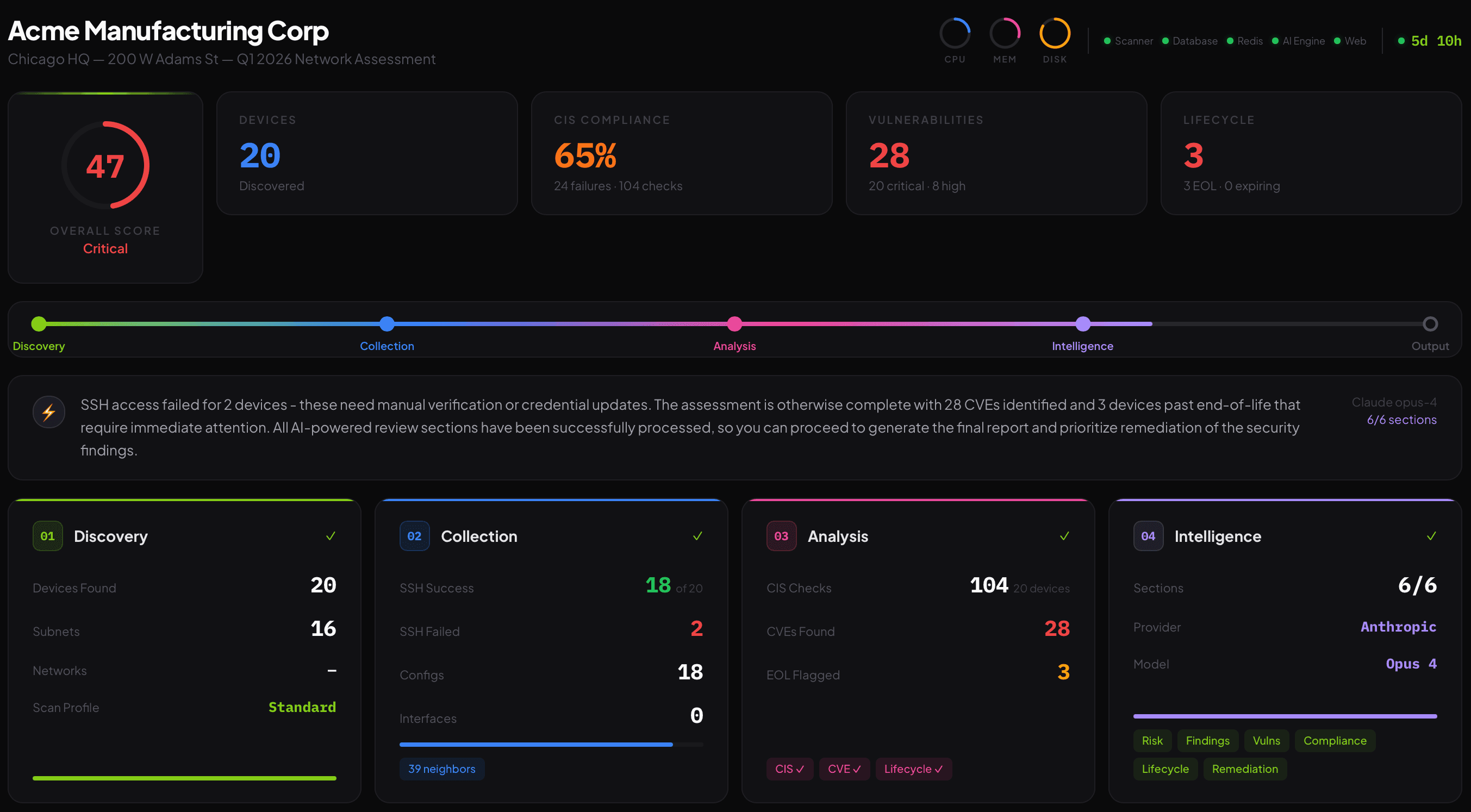
Complete infrastructure posture in a single view
Real-time assessment progress — overall security score, device inventory, CIS compliance, vulnerabilities, lifecycle risk — with AI-generated status briefings.
- Overall security score with color-coded severity
- 5-phase progress tracking with live status
- AI-generated situation briefing
- CIS / CVE / EOL KPI scorecards
- System health gauges (CPU, memory, disk)
- Multi-assessment support with instant switching
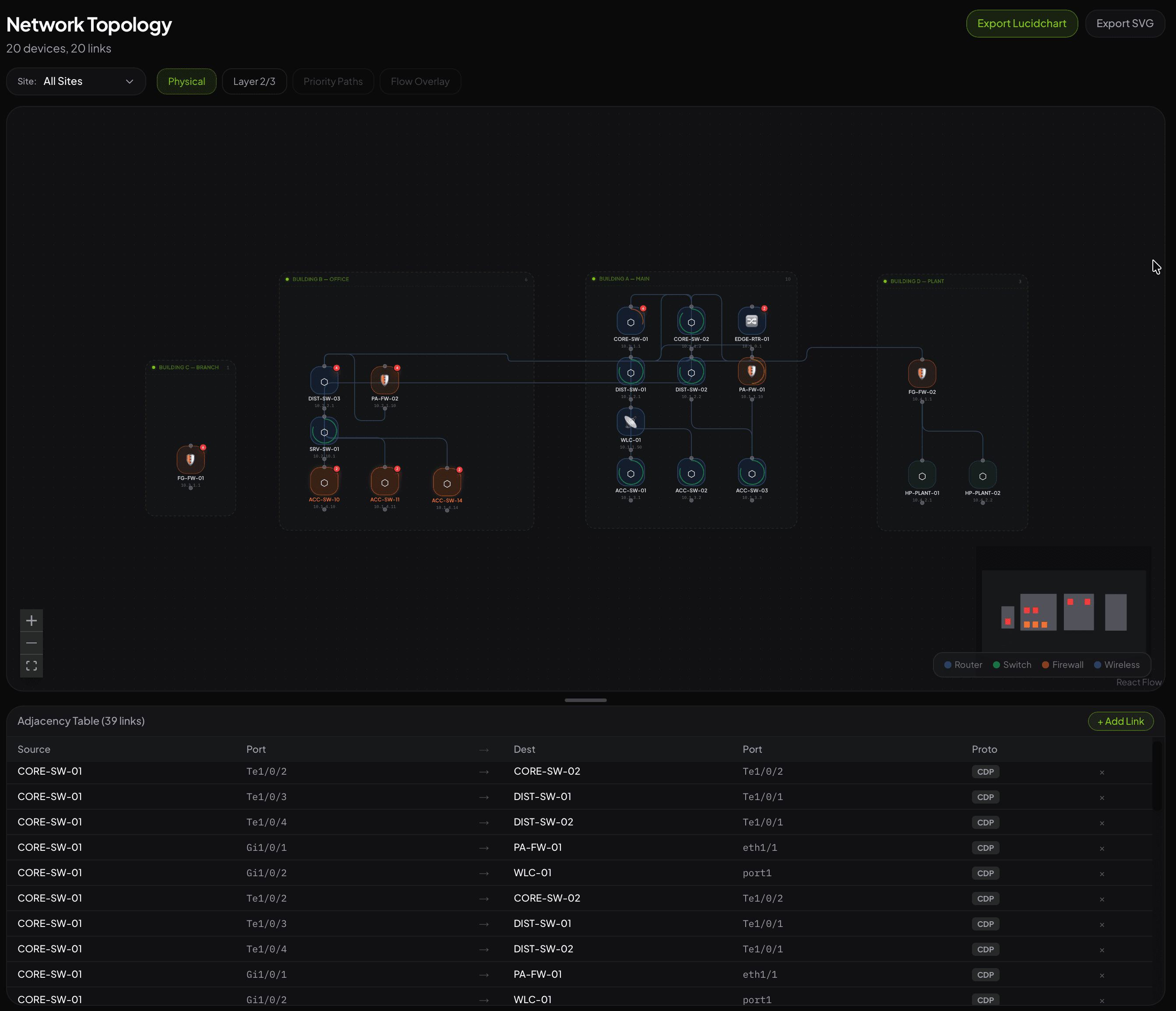
Interactive infrastructure mapping
Automatically builds a topology from CDP/LLDP neighbor discovery. Drag nodes, group by site, visualize risk. Export to Lucidchart for executive deliverables.
- Auto-layout by device tier (firewall → core → access)
- Site grouping with drag-and-drop assignment
- Color-coded by EOL status and vulnerability count
- Editable adjacency table for manual connections
- One-click Lucidchart / draw.io export
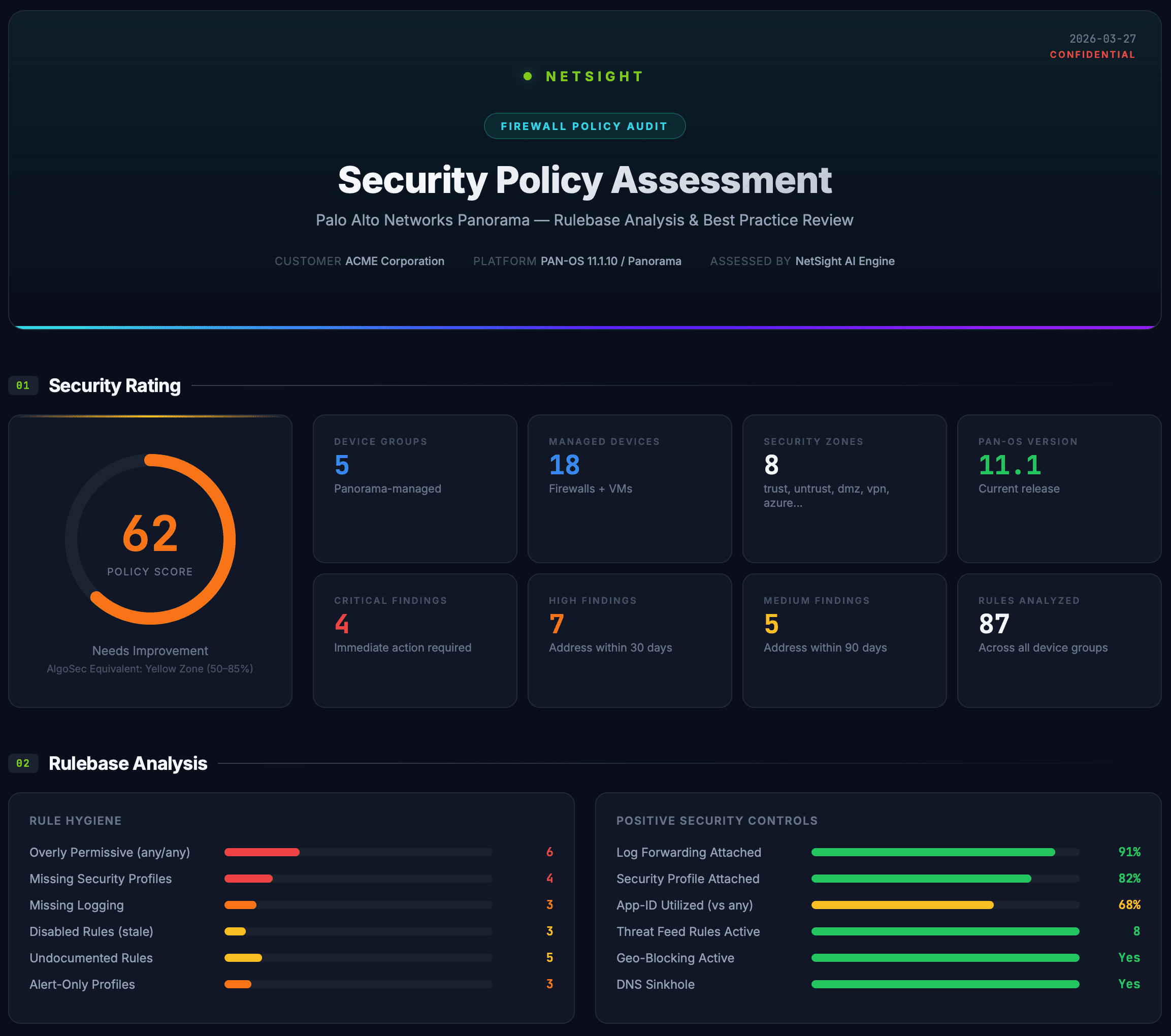
AlgoSec-grade policy analysis, automated
Upload a firewall config or pick a device from inventory. AI analyzes the rulebase, profile coverage, platform hardening, and compliance posture — producing a report with scoring, findings, and remediation.
- Palo Alto, Fortinet, Cisco ASA, Meraki
- Rulebase hygiene and best-practice heatmap
- Profile coverage analysis (AV, IPS, URL, WF)
- Compliance mapping (PCI DSS, NIST, CIS)
- AI-generated risk narrative per device
- PDF output with scoring and remediation roadmap
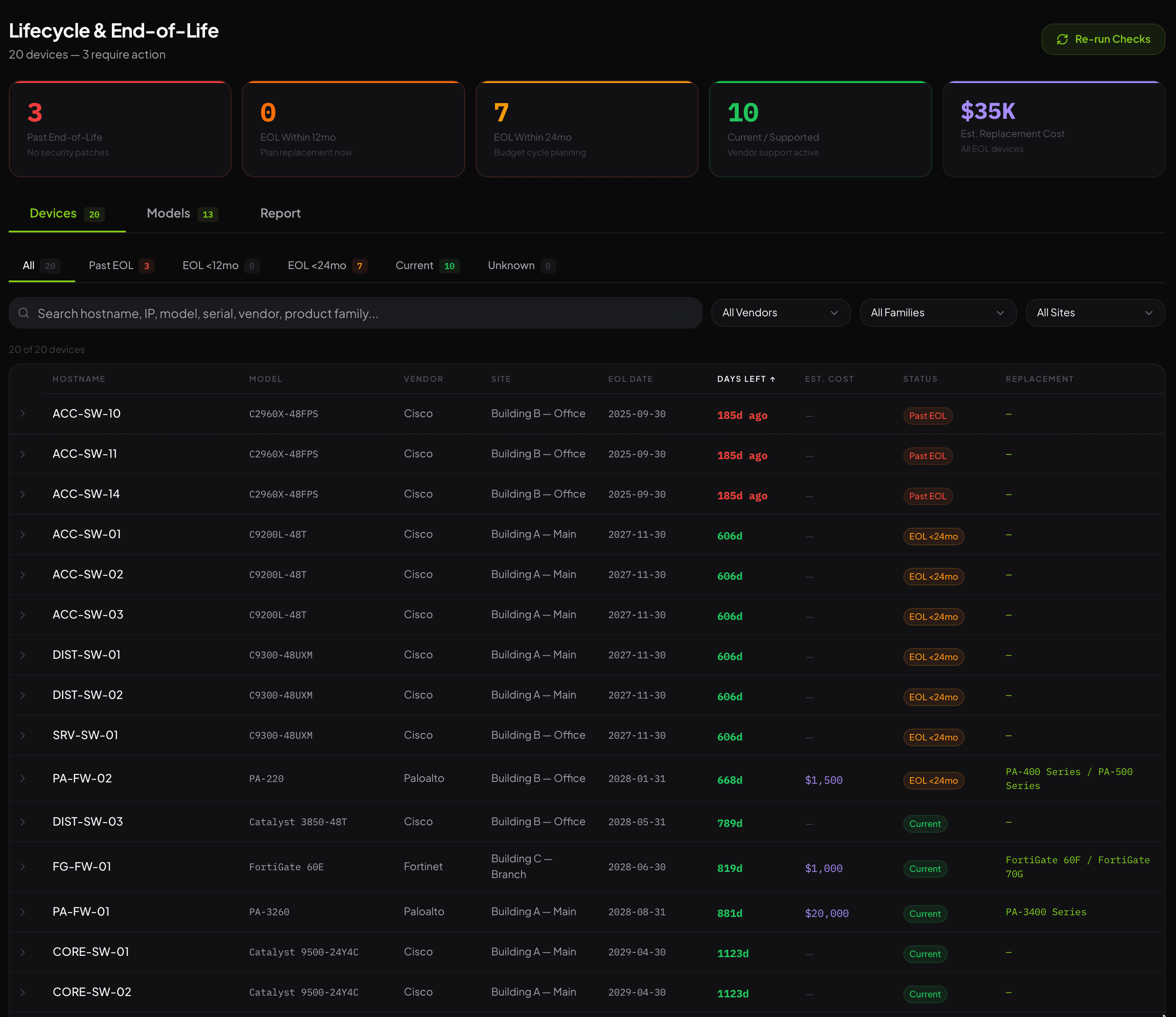
608 models. 6 vendors. 9 milestones.
Automatic EOL matching with budget forecasting, compliance risk mapping, and replacement planning. Editable per-model overrides for organization-specific pricing.
- Cisco, Palo Alto, Fortinet, Juniper, Aruba, Ubiquiti
- 9 lifecycle milestones per device (EoSale → EOL)
- PID-level matching from vendor bulletins
- Budget forecast with 5-year CapEx projection
- Compliance mapping: PCI DSS, NIST, HIPAA, SOX
- Dedicated lifecycle report with AI narrative
Everything you need to secure your infrastructure
Comprehensive infrastructure security — from first scan to executive report.
Network Discovery
Nmap-powered scanning with smart profiles — quick, standard, deep, stealth. SNMP, SSH banner grab, and service fingerprinting.
Config Collection
SSH and NETCONF pull running configs, interface state, routing tables, neighbor tables. 14 data getters per device.
CIS Benchmarking
Automated CIS benchmark checks against Cisco IOS-XE, Palo Alto PAN-OS, and Fortinet FortiOS. Per-device pass/fail with evidence.
Vulnerability Matching
CVE correlation against discovered OS versions. CVSS scoring, exploitability context, and pre-auth detection from Nmap NSE.
Firewall Policy Audit
AlgoSec-competitive analysis for PA, Fortinet, ASA, Meraki. Rulebase hygiene, profile heatmap, compliance mapping.
Lifecycle Management
608-model EOL database across 6 vendors. 9 milestones tracked. Budget forecasting, replacement planning, compliance risk.
AI-Powered Analysis
Claude Opus 4.6 (1M context) or local Ollama. 7 narrative sections — risk, findings, vulns, compliance, lifecycle, remediation.
Executive Reports
Executive, Technical, Firewall Audit, and Lifecycle reports. HTML, PDF, DOCX, PPTX. Custom brand kits with your logo and colors.
Portable Deployment
Single Docker Compose stack — runs anywhere with no internet. Azure VM, on-prem, or any site. 10 minutes to first scan.